Write A Complete Report On Intrusion Detection Systems.
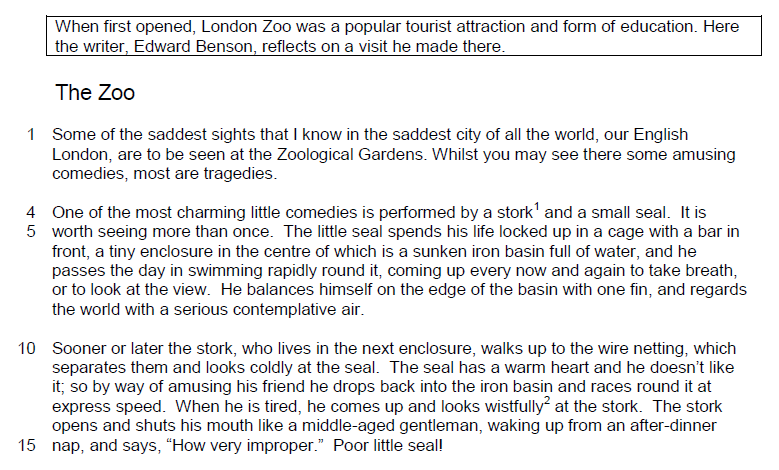
Intrusion Detection System (IDS) is a system which is used to detect and report the malicious activity in the ad hoc networks .IDS can collect and analyze data for the entire network. Critical node is a node whose failure or malicious behavior disconnects or significantly degrades the performance of the network .Packets may be dropped due to network congestion.
Intrusion detection systems such as SNORT are quite capable of detecting some of the known data link layer attacks and include a mechanism for integrating Intrusion Prevention System (IPS) solutions. This paper does not advocate against the use of these solutions in organizations.
An intrusion detection system (IDS) is a device or software application that monitors a network or systems for malicious activity or policy violations. Any intrusion activity or violation is typically reported either to an administrator or collected centrally using a security information and event management (SIEM) system. A SIEM system combines outputs from multiple sources and uses alarm.
Testing carried out in compliance with EN1317-2: 1998 measured the VI to the maximum dynamic lateral position of the HGV (i.e. H1, H3, H4a and H4b vehicles), which may have had a flat bed, a curtain sided or a box sided construction, e.g. if a flat-bed vehicle was used then the VI would have likely been the same or slightly greater than the WW of the VRS.
Intrusion Detection Systems. We provide complete Intrusion Detection Systems designed to assess and deter threats rapidly and improve incident analysis. We deploy effective and reliable detection systems from very simple to extremely demanding environments. Passive infrared and microwave; Radar and sonar; Smart fence, ported coaxial cable.
This Research Paper on Detection and Prevention of Wireless Intrusion was written and submitted by user Nathalie Hawkins to help you with your own studies. You are free to use it for research and reference purposes in order to write your own paper; however, you must cite it accordingly.
Android App for storing complete report of Intrusion Detection System(IoT Device based on Raspberry Pi along with Firebase for Database)) 14 commits 1 branch 0 packages 0 releases Fetching contributors Java. Java 100.0%; Branch: master. New pull request Find file. Clone or download.